On January 20, the European Commission published COM(2026) 13 — a proposed directive amending NIS2 with the first explicit post-quantum cryptography requirement in EU law. Member States must adopt dedicated PQC transition policies. The NIS Cooperation Group roadmap sets the milestones: begin transitioning by end of 2026, critical infrastructure by 2030, everything else by 2035.
Germany has been ahead of this for years. BSI’s TR-02102-1 recommends hybrid PQC for key exchange today, mandates it by 2032, and names the algorithms. BSI co-chaired the EU roadmap working group. The guidance is thorough, conservative, and correct.
We scanned bsi.bund.de.
BSI: Grade B
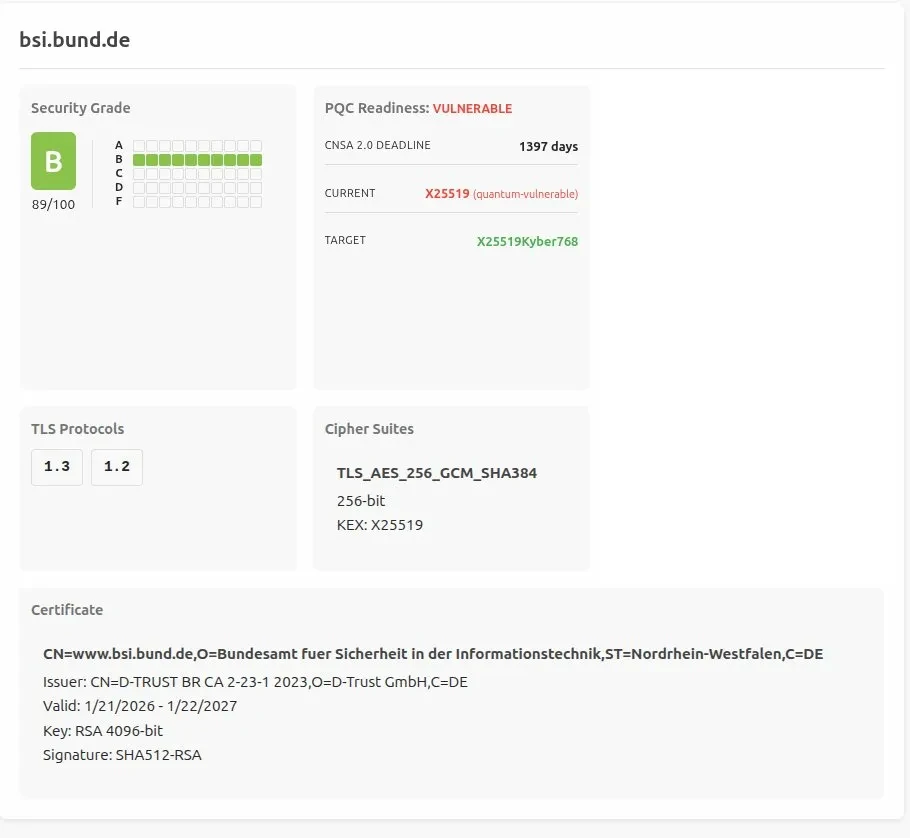
Key exchange: X25519. Quantum-vulnerable. The classical algorithm TR-02102-1 says should not be used alone after 2031. No ML-KEM. No hybrid. The certificate is RSA 4096-bit, SHA512-RSA, issued by D-TRUST. Classical everything.
Grade B means strong TLS hygiene — good ciphers, current protocols, nothing broken. But no post-quantum key exchange. The grade reflects competent conventional cryptography and zero PQC deployment.
Bundesbank: Grade A
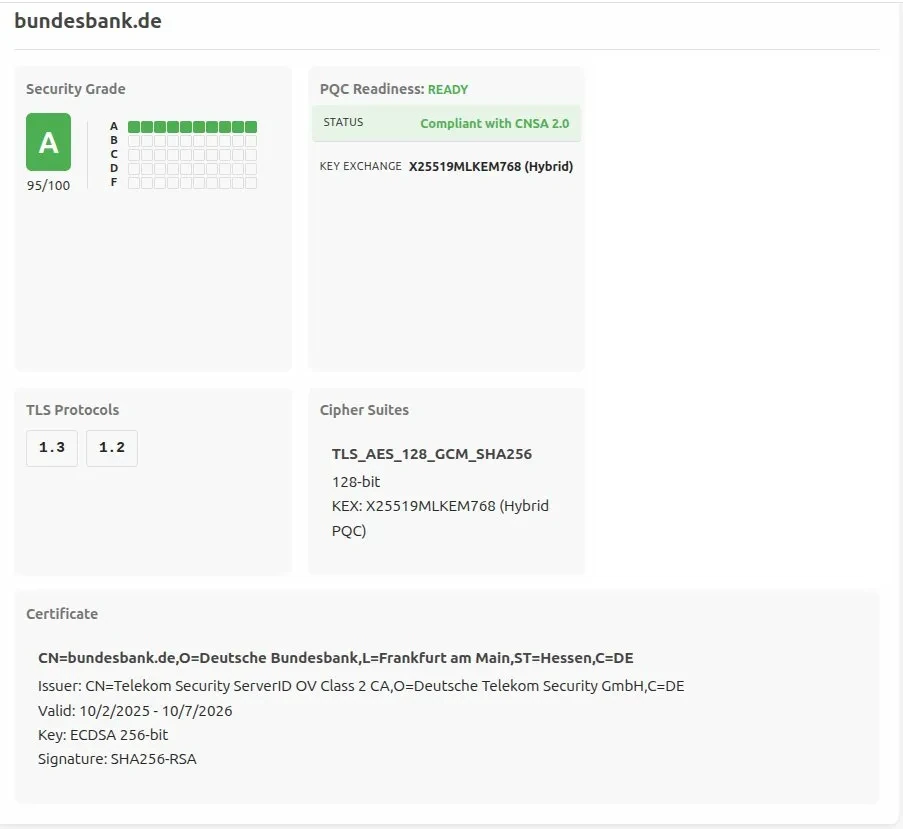
One sector over — Banking, same NIS2 Annex I — bundesbank.de tells a different story.
Key exchange: X25519MLKEM768. Hybrid PQC. The exact algorithm combination BSI recommends in TR-02102-1.
Grade A means everything a B has, plus post-quantum key exchange. The grade history is ten straight A’s. Germany’s central bank followed BSI’s guidance. BSI did not follow its own.
Who Has PQC, Who Doesn’t
We scanned NIS2 Directive sectors — Banking, Energy, Health, Transport, Digital Infrastructure, Public Administration — and checked whether each server negotiates ML-KEM or X25519Kyber768 hybrid key exchange. The algorithms that BSI, NIST, and the EU roadmap all converge on.
In Banking, Bundesbank and Commerzbank negotiate hybrid PQC. Deutsche Bank does not — and scores an F on basic TLS hygiene as well. The rest of the sector is classical.
In Public Administration, the split follows a pattern. The politically visible domains — bundeskanzler.de, bundesregierung.de, bundestag.de, auswaertiges-amt.de — negotiate hybrid PQC. The security and regulatory agencies — BSI, BKA, Verfassungsschutz, Bundespolizei, BFDI — do not. Neither does personalausweisportal.de, the endpoint for the identity infrastructure Germany is building the EUDI Wallet on.
In Digital Infrastructure, the PQC adoption that exists comes from upstream. Google, Cloudflare, and a handful of other hyperscalers enabled ML-KEM server-side in 2024. German telecom and hosting infrastructure has not followed. Telekom.de: no PQC. Vodafone.com: no PQC.
In Energy, Health, and Transport, PQC adoption is negligible.
An international comparison is instructive. gov.uk — the UK government site maintained by the NCSC — negotiates hybrid PQC. The German federal government has it on the Chancellor’s site but not on the cybersecurity agency’s.
Flat Lines
In February, we showed that Cloudflare’s reported PQC adoption measures browser auto-upgrades, not server-side policy. Edge adoption climbed because Chrome shipped ML-KEM by default. Origin servers didn’t move.
The NIS2 sectors show the same pattern, inverted. This isn’t edge versus origin — it’s origin versus origin, within the same regulated sectors. The trajectories are flat.
| Target | Sector | PQC | Grade History |
|---|---|---|---|
| bundesbank.de | Banking | YES | A A A A A A A A A A |
| deutsche-bank.de | Banking | NO | F F F F F F F F F F |
| bsi.bund.de | Public Administration | NO | B B B B B B B B B B |
| bundeskanzler.de | Public Administration | YES | A A A A A A A A A A |
Nobody is in transition. The endpoints that enabled PQC did so in a single configuration change and stayed there. The endpoints that haven’t are flat at zero with no movement. COM(2026) 13 says begin transitioning by end of 2026. There is no transition underway to begin.
The Gap Between Plan and Execution
There’s a familiar argument that PQC migration is premature while basic encryption adoption remains poor. That sequence sounds logical but the scan data contradicts it. Bundesbank didn’t master classical cryptography and then graduate to PQC. They configured hybrid key exchange. It’s a deployment decision, not a curriculum. Deutsche Bank hasn’t deployed either — classical TLS is broken and PQC is absent. The organizations that enabled post-quantum did it in a single configuration change. The organizations that haven’t aren’t building toward it. They’re stationary.
Every one of these frameworks starts with the same first step: know what you’re running. Cryptographic inventory. BSI says it. CISA says it. The NIST NCCoE built a workstream around it. The BSI/KPMG market survey sent questionnaires to 150 German organizations asking about their quantum readiness. Twenty-eight responded. BSI called the results “worrying.”
We didn’t send a questionnaire. We ran a scan.
The plan is done. The deadlines are set. The guidance is published. Execution hasn’t started — not even at the agency that wrote the guidance.
Scan your own infrastructure at pqprobe.com. Probe endpoints, source code, dependencies, and filesystems for quantum-vulnerable cryptography, with compliance mapping to NIS2, CNSA 2.0, and PCI DSS.